Solutions for security by design
Securing automation and IT systems against cyberattacks and manipulation is a top priority in almost every plant and project. However, many operators lack the required expertise to identify risks and threats. The good news: suitable solutions are now available that can be easily adapted to the individual project requirements to provide optimum security.
What happened with the WannaCry ransomware, as drastic as the effects were, was but a warning shot to plant operators and systems integrators: The worldwide cyberattack is estimated to have affected more than 10000 organizations and some 200000 computers across 150 countries. Especially troubling to IT and security experts is that the crypto worm used a known exploit that could have been closed with patches. However, many organizations had not applied them or were running legacy systems that could no longer be patched.
A serious reminder of a serious issue
WannaCry is just one example of a growing number of cyberattacks – and while malware that specifically targets industrial control systems is still rare, automation and control systems are already more networked with general IT systems than many plant operators realize. Having good, regular and secure backups, using appropriate software, implementing good cybersecurity including isolating critical systems, and always having the latest security patches installed should be a given.
In its whitepaper on cybersecurity, the ARC Advisory Group lists several barriers to improving cybersecurity in industrial environments. They include increasingly open industrial automation, insufficient awareness among end-user management, increased use of commercial off-the-shelf IT solutions, inadequately trained staff, and misconceptions concerning the cybersecurity life cycle.
ARC believes organizations are reluctant to act on potential threats and to adopt security planning and implementation because the task appears too daunting. Furthermore, in the customized control environment of an industrial site, it is difficult to predict how a newly introduced patch will impact the functioning of the control system, especially if the patch is not tested rigorously.
Industrial security as specified in recent guidelines, such as the IEC 62443, should therefore be treated as a life cycle concern consisting of five phases: product or system development, specification, integration & commissioning, operations & maintenance, and decommissioning.
The phases require clear accountability and coordinated communication between different roles and stakeholders such as system integrators, product suppliers and asset owners.
A blueprint for securing assets and systems
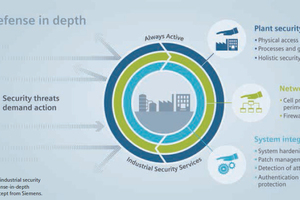
A defense-in-depth security approach covering a heterogeneous and broad range of security topics – including network security, user authentication, secure configuration and the hardening of operating system, logging, encryption, and secure channels – is required. Technical solutions and tools are available, but project teams often lack the time and expertise to choose a suitable solution for each security topic. Hence, a common pitfall is to focus on some topics in detail while overlooking others.
In November 2018, Siemens became the first company in the world to gain TÜV certification for the secure system integration of process automation and drives systems in compliance with the international IEC 62443-2-4 standards. Based on this standard, Siemens has developed several blueprints for automation and control systems engineering to facilitate security engineering and eliminate potential security weak spots. These blueprints provide guidance in the form of references to specific resources and make sure that the engineering project produces all security documents. For example, the Siemens minerals solution blueprints for conventional mill drives and gearless mill drives have been developed according to these blueprints.
In the end, designs that fulfill IEC 62443 simplify information exchanges between stakeholders and deliver a complete set of documents for acceptance tests and the security solution certification.
Security through expertise
The development of the secure framework and the secure project blueprints was driven by Siemens’ own experience. Key areas of importance include helping the asset owner identify critical assets and specify suitable protection goals; supporting the security life cycle process through an efficient threat and risk analysis; implementing efficient and effective testing and compiling; and providing the required documentation.
Particularly in large projects where security affects different disciplines – such as network, software applications and firmware – the framework establishes a common language for engineers to work together on security. On an organizational level, the framework also facilitates the communication between units that develop components and those that work as system integrators and on service.
The security framework combines the expertise of Siemens security engineers and incorporates them into a reproducible process that yields reproducible results – thus mitigating project risks. As the blueprints are based on a comprehensive Simatic PCS 7 security standard, the secure solution can be easily designed to cover all required assets and security levels. Plant operators benefit by having a security solution engineered for their specific requirements that is ready for certification according to IEC 62443. During plant operation, the security documents support system maintenance.
As cyberthreats become more frequent and more creative, industry players are developing and deploying more sophisticated cybersecurity systems and procedures to meet ever-changing requirements. Supported by their own specialist organizations, a global network of experts for automation and cybersecurity monitors current and developing threats, analyses solutions for weaknesses, and develops suitable measures, thus making sure that their control and automation solutions are and continue to be secure by design.
$(LEhttp://